Detect compromised data. Expose hidden cyber threats.
Monitor non-indexed channels, dark web, and closed forums for leaked credentials, stolen data, and cloned sites. Detect hidden risks and illicit links early to prevent breaches and ensure compliance.
PAIN POINTS
Why do teams need dark web visibility?
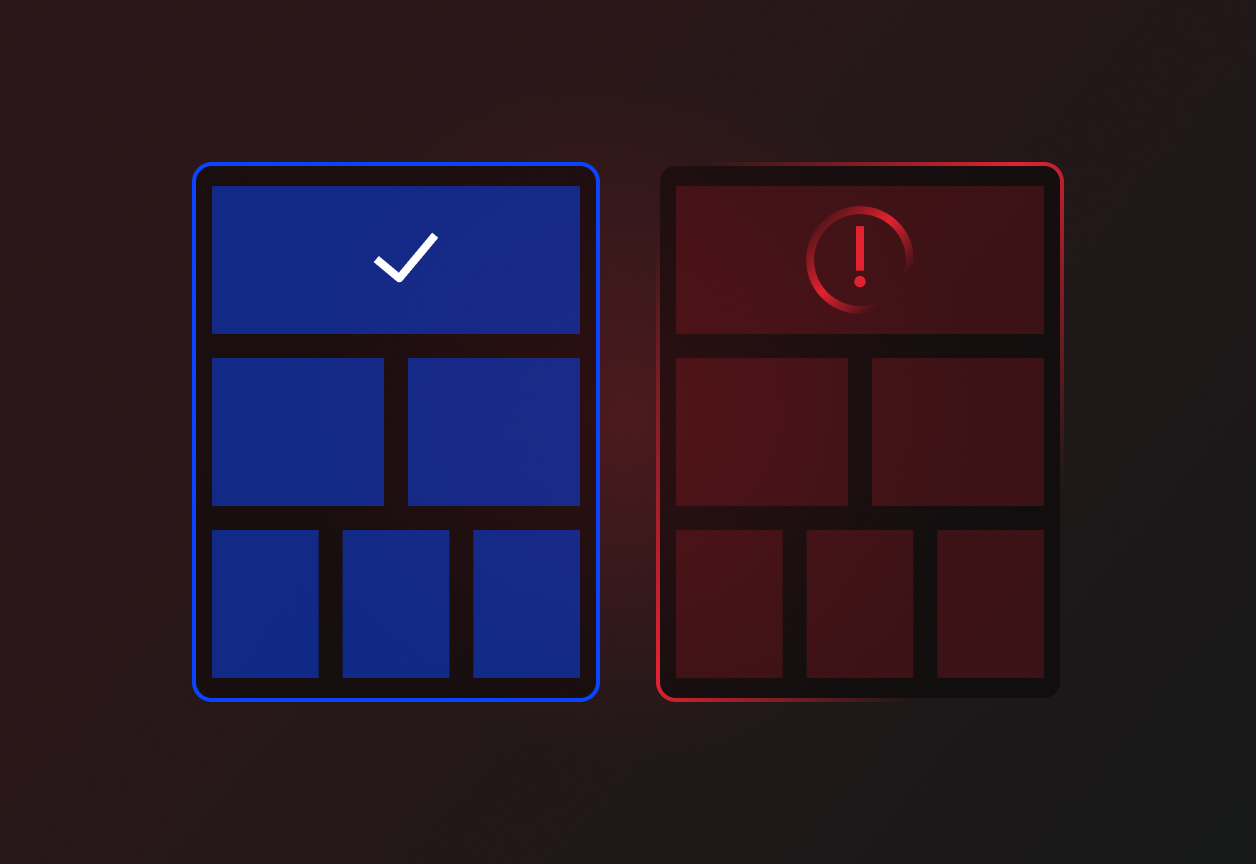
Surface-level checks miss compromised data. Dark/Deep Web Monitoring exposes it.
Illuminate compromised environments
Merchant data breaches occur far outside of indexed search engines. Without visibility into closed networks, you risk supporting merchants tied directly to compromised payment environments.
Detect and block data leaks early
Stolen customer data, leaked credentials, and card dumps circulate freely on the dark web. Overlooking these early warning signs inevitably leads to massive fraud losses and chargebacks.
Ensure strict cybersecurity compliance
Regulators and card schemes demand strict cybersecurity vigilance. Failing to monitor non-indexed environments for merchant impersonation leaves your acquiring license exposed to PCI-DSS and GDPR penalties.
SOLUTIONS
How Dark/Deep Web Monitoring solves these problems?
Scans non-indexed threat intel channels to deliver proactive, early-warning cyber alerts.
Continuous Threat Intel Scanning
Monitor dark web marketplaces, paste sites, and closed-network forums continuously for early fraud signals. Detect leaked merchant credentials, stolen customer data, BINs, and exposed payment details instantly. Flag illicit mentions of your approved merchant brands directly within active carding markets and fraud forums.
Expose Brand Impersonation
Identify cloned merchant sites, highly sophisticated impersonation domains, and active phishing attempts. Discover merchant-related leaks or impersonations 3x faster than manual, surface-level investigations. Reduce the severe reputational risk of cloned merchant sites and brand abuse by up to 70%.

Proactive Cyber Compliance
Export actionable alerts featuring exact source links, timestamped screenshots, and complete threat summaries. Cross-check incident sources by integrating intelligence directly into your existing KYM workflows. Align your portfolio defense strictly with complex PCI-DSS, BRAM, GDPR, and card scheme cybersecurity mandates.
WHO IT’S FOR?
One tool helps multiple teams achieve their goals. Connect your departments with a single, shared platform.
Security
Detect severe merchant exposure and compromised payment environments before they impact cardholders or operations.
Compliance & Legal
Strengthen your institutional cyber-readiness and enforce strict adherence to complex PCI-DSS and scheme mandates.
Operations
Flag at-risk or definitively breached merchants instantly for immediate remediation and portfolio quarantine.
Risk & Fraud
Cross-check complex incident sources tied to merchant activity using real-world, non-indexed threat intelligence.
Ready to take control of merchant risk?
See how Onlayer fits your workflow in a short demo.